Introduction: Securing Your Business in an Evolving Threat Landscape
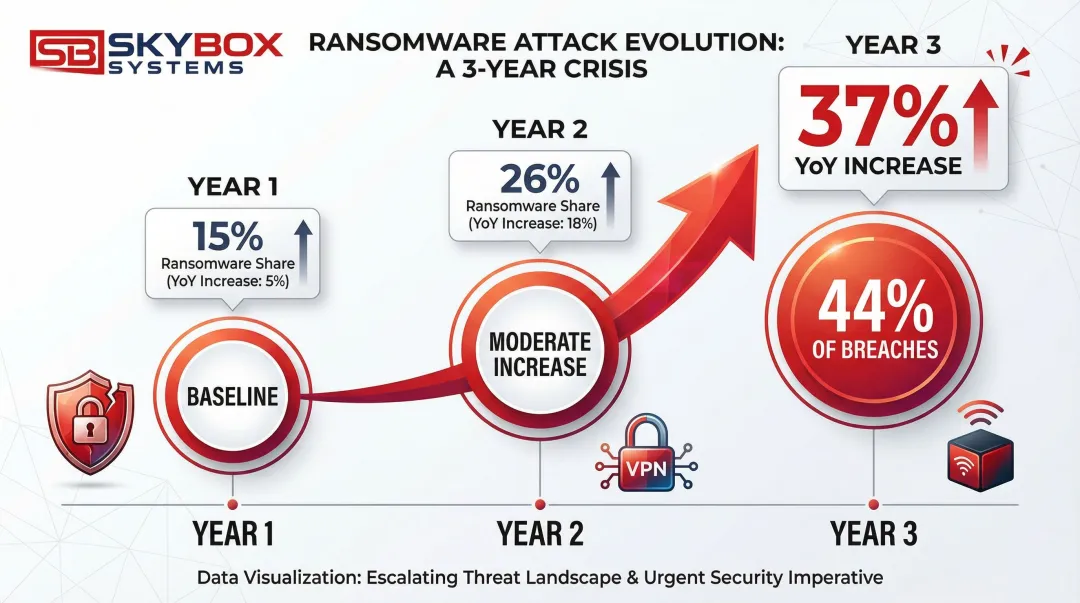
Data breaches now cost businesses an average of $4.44 million, while ransomware attacks have surged 37% year-over-year. Attackers are exploiting vulnerabilities in VPNs and edge devices at unprecedented rates, targeting the very tools businesses use to enable remote work.
The threat landscape presents critical challenges:
- Global cybersecurity workforce gap: 5.5 million unfilled positions
- 67% of organizations report staff shortages in security roles
- Small to mid-sized businesses struggle to hire qualified security professionals
These resource constraints leave critical vulnerabilities unaddressed.
Protecting your digital infrastructure requires a foundation of secure, reliable network and physical security systems. From structured cabling that forms the backbone of your network to integrated access control and video surveillance, the physical infrastructure determines how well your business can defend against threats and respond to incidents.
TLDR: Key Takeaways
- MSSPs provide outsourced cybersecurity monitoring, management, and incident response
- 24/7 monitoring costs $45-$73 per endpoint monthly versus millions in-house
- Core services: firewall management, intrusion prevention, SIEM monitoring, and compliance
- Choose providers with SOC 2/ISO 27001 certifications, clear SLAs, and compliance expertise
- Most valuable for businesses with talent gaps, compliance needs, or remote work security
What Are Managed Network Security Services?
Managed network security services are comprehensive cybersecurity solutions delivered by third-party Managed Security Service Providers (MSSPs) who monitor, manage, and protect business networks and digital assets around the clock.
Unlike general IT support that focuses on system uptime and maintenance, MSSPs specialize in security threats, vulnerabilities, and compliance.
Gartner defines an MSSP as a provider offering "outsourced monitoring and management of security devices and systems." This includes managed firewalls, intrusion detection, VPN, and vulnerability scanning.
Service Delivery Model
MSSPs typically operate on a subscription-based model, converting large capital expenditures into predictable monthly operational costs. Services are delivered through:
- Security Operations Centers (SOCs) providing 24/7/365 monitoring of network traffic and security events
- Remote management of security infrastructure with optional on-site support for complex issues
- Co-managed approaches where MSSPs complement internal IT teams with specialized expertise
Evolution of Managed Security
Managed security has evolved significantly from early firewall management services:
- First Generation: Basic device management for firewalls and VPNs
- Second Generation: Log collection and alerting through SIEM platforms
- Current Generation: Managed Detection and Response (MDR) using AI and machine learning to actively contain threats in real-time, not just alert on them
Today's MSSPs provide comprehensive protection across endpoints, cloud environments, applications, and even integrate with physical security systems.
They don't replace internal IT functions but enhance capabilities with specialized expertise that most businesses cannot maintain independently.
Why Businesses Need Managed Network Security Today
Ransomware and Sophisticated Threats
Ransomware now appears in 44% of all analyzed breaches, representing a 37% increase from the previous year.
Attackers are increasingly exploiting vulnerabilities in edge devices and VPNs—the very tools businesses rely on for remote access. These exploits have grown nearly eight-fold compared to previous years, demonstrating how rapidly attack methods evolve.
Beyond ransomware, businesses face:
- Zero-day exploits targeting unpatched vulnerabilities
- Sophisticated phishing campaigns that bypass traditional filters
- Insider threats from compromised credentials
- Supply chain attacks that infiltrate through trusted vendors
The Cybersecurity Skills Crisis
These evolving threats require skilled defenders, but finding them is increasingly difficult.
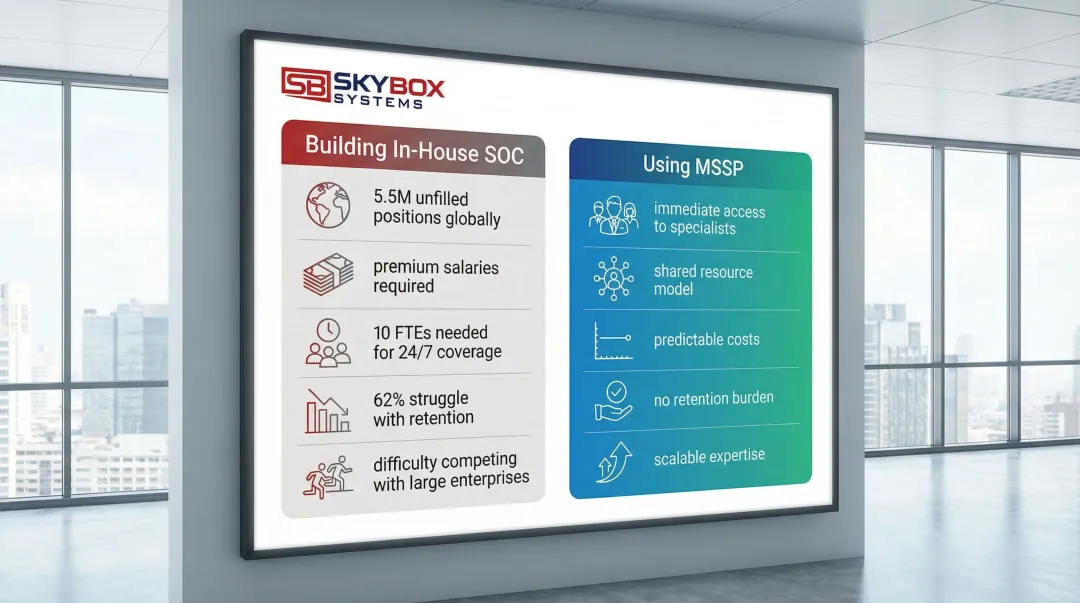
The talent shortage has reached crisis levels. 5.5 million cybersecurity positions remain unfilled globally, and 31% of security teams have zero entry-level professionals. The pipeline for future talent is broken.
For small to mid-sized businesses, the challenge is even more acute:
- Qualified security analysts command premium salaries that most SMBs cannot afford
- Retention is difficult when larger organizations offer better compensation
- 62% of SOC professionals believe their organizations struggle to retain top talent
- Building a 24/7 SOC requires approximately 10 full-time employees just for shift coverage
Compliance and Regulatory Requirements
Modern compliance frameworks demand continuous monitoring, not annual audits. Industries face increasingly strict regulations requiring documented security controls:
- HIPAA requires covered entities to "implement procedures to regularly review records of information system activity, such as audit logs, access reports, and security incident tracking reports" (45 CFR § 164.308)
- PCI DSS mandates continuous monitoring and log review to protect cardholder data
- GDPR requires appropriate technical measures to ensure security appropriate to the risk
MSSPs provide the technical controls, continuous monitoring, and audit documentation these regulations demand—capabilities that are operationally burdensome for internal teams to maintain.
Expanded Attack Surfaces from Remote Work
Compliance concerns intensify as work environments grow more distributed.
The shift to remote and hybrid work has eliminated the traditional network perimeter. Employees access corporate resources from home networks, coffee shops, and personal devices.
This expanded attack surface creates new vulnerabilities that attackers aggressively target.
The Verizon DBIR notes a massive increase in attacks targeting VPNs and edge devices—precisely the infrastructure enabling remote work. Without proper security monitoring and management, these access points become entry vectors for attackers.
Business Continuity and Financial Risk
A single successful attack can devastate a business. The $4.44 million average breach cost is just the beginning.
Organizations also face:
- Operational downtime that halts revenue generation
- Regulatory fines for compliance violations
- Legal fees and potential lawsuits
- Customer loss and reputation damage
- In severe cases, business closure
For businesses operating on thin margins, these costs can be existential threats that managed security services help prevent.
Core Components of Managed Network Security Services
Managed Firewall Services
Firewalls control network traffic flow based on security policies, acting as the first line of defense against external threats.
Managed firewall services involve expert configuration, continuous monitoring, and rule optimization by security specialists.
MSSPs handle:
- Firmware updates and security patches to address newly discovered vulnerabilities
- Policy adjustments as business needs change or new threats emerge
- Traffic analysis to identify suspicious patterns indicating potential attacks
- Alert response and investigation when security events occur
- Performance tuning to maintain business functionality while maximizing security
This approach eliminates the need for internal expertise in complex firewall platforms while ensuring configurations follow security best practices.
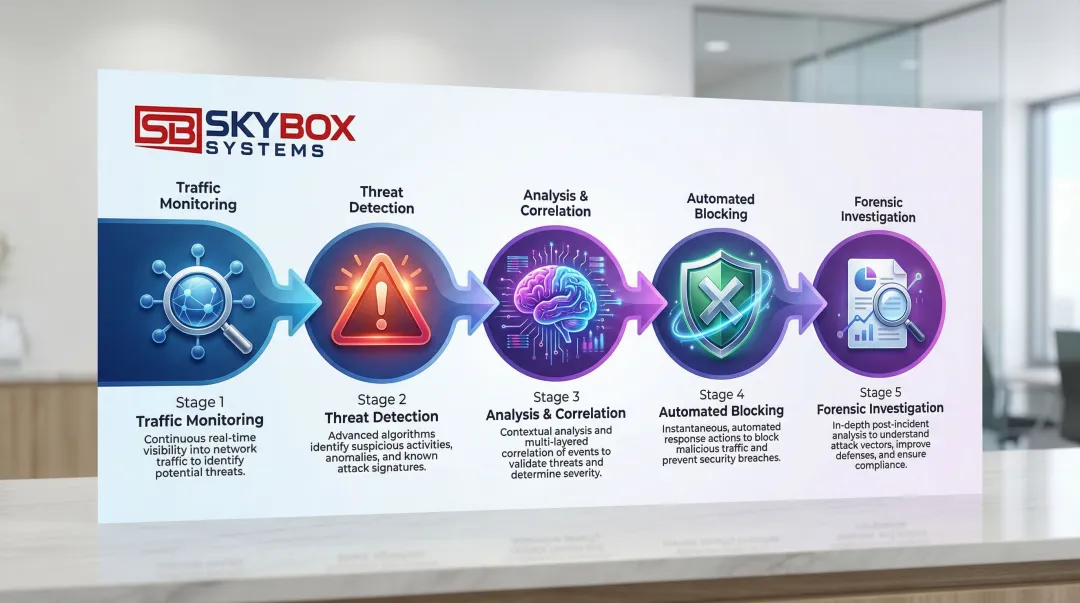
Intrusion Detection and Prevention Systems (IDS/IPS)
Intrusion Detection Systems (IDS) monitor network activity to identify suspicious patterns and potential threats. Intrusion Prevention Systems (IPS) go further by actively blocking malicious traffic before it can cause damage.
Managed IDS/IPS services provide:
- Current threat signatures updated as new attacks emerge
- Expert analysis to reduce false positives that waste time investigating legitimate activity
- Actionable intelligence about attack attempts, including source, methods, and targets
- Automated blocking of known malicious traffic patterns
- Detailed forensic data for incident investigation
Virtual Private Network (VPN) Management
VPNs create secure, encrypted connections for remote workers and site-to-site communications. Given the recent increase in VPN-targeted attacks, professional management is critical.
Managed VPN services ensure:
- Proper encryption protocols that meet current security standards
- Access controls limiting who can connect and what resources they can access
- Performance optimization balancing security with user experience
- Monitoring for unauthorized access attempts or compromised credentials
- Regular security audits of VPN configurations
Security Information and Event Management (SIEM)
SIEM platforms collect, correlate, and analyze security events from across the entire IT environment—firewalls, servers, endpoints, applications, and cloud services. This centralized visibility helps identify complex threats that single-point solutions might miss.
Managed SIEM services provide:
- 24/7 monitoring of aggregated security events across all systems
- Correlation analysis that connects seemingly unrelated events to identify attacks
- Incident investigation by experienced analysts who understand threat patterns
- Compliance reporting with documented evidence of security monitoring
- Threat intelligence integration that adds context about emerging attacks
Without an MSSP, businesses face significant challenges. They must invest in expensive SIEM platforms and hire specialized analysts to interpret the massive volume of data these systems generate daily.
Vulnerability Management and Patch Monitoring
Attackers constantly scan for unpatched systems and known vulnerabilities. Vulnerability management involves identifying these weaknesses before attackers can exploit them.
Managed vulnerability services include:
- Regular automated scans of systems, applications, and network devices
- Prioritization of discovered vulnerabilities based on severity and exploitability
- Patch tracking to identify missing security updates
- Testing protocols to ensure patches don't disrupt business operations
- Remediation guidance for vulnerabilities that cannot be immediately patched
This proactive approach closes security gaps that attackers actively target, particularly in edge devices and remote access infrastructure.
Endpoint Detection and Response (EDR)
EDR solutions protect individual devices—computers, servers, mobile devices—by monitoring for suspicious behavior and enabling rapid response to compromised endpoints.
Managed EDR extends protection beyond the network perimeter to every device accessing business resources:
- Behavioral analysis that detects ransomware encryption attempts in real-time
- Automated isolation of compromised devices to prevent lateral movement
- Forensic investigation capabilities to understand attack scope
- Threat hunting to proactively search for hidden threats
- Remote remediation to clean infected devices without on-site visits
Remote work scenarios demand this level of protection, as devices operate outside traditional network security controls.
Benefits of Outsourcing Network Security Management
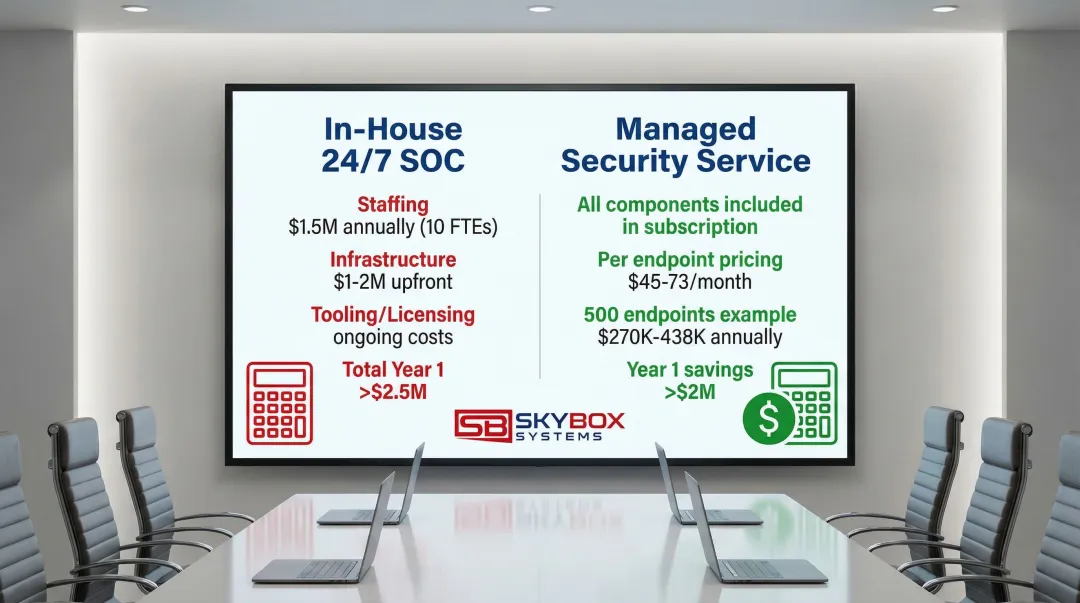
Cost Efficiency Compared to In-House SOCs
Building a 24/7 Security Operations Center internally requires massive investment that most SMBs cannot justify:
| Cost Component | In-House 24/7 SOC | Managed Security Service |
|---|---|---|
| Staffing | ~$1.5 million annually (10 FTEs for true 24/7 coverage) | Included in subscription |
| Infrastructure | $1-2 million upfront CAPEX | Included in subscription |
| Tooling/Licensing | Significant ongoing costs | Included in subscription |
| Total Year 1 | >$2.5 million | $45-$73 per endpoint/month |
For an organization with 500 endpoints, an MSSP subscription costs approximately $270,000-$438,000 annually—saving over $2 million in the first year compared to building a full internal SOC.
Beyond the dramatic cost savings, the subscription model converts large upfront capital expenditures into predictable monthly operational expenses that scale with business needs.
24/7/365 Monitoring Capabilities
Cyber attacks don't respect business hours. 79% of SOCs operate 24/7, but maintaining this coverage internally requires approximately 10 full-time employees to cover shifts, vacations, and turnover.
MSSPs leverage shared resources across multiple clients to provide true round-the-clock monitoring that detects threats regardless of when they occur. Continuous monitoring delivers:
- Immediate detection of after-hours attacks when internal staff aren't available
- Faster response times that limit damage and reduce breach costs
- Weekend and holiday coverage without overtime expenses
- Consistent monitoring quality across all shifts
Access to Specialized Expertise
Beyond cost savings and round-the-clock coverage, MSSPs provide access to specialists in digital forensics, threat intelligence, and incident response—roles that are scarce and expensive to hire:
- Certified professionals with credentials like CISSP, CEH, and vendor-specific certifications
- Threat hunters who proactively search for hidden compromises
- Incident responders trained in containment and recovery procedures
- Compliance specialists who understand industry-specific regulations
With 62% of SOC professionals believing their organizations struggle to retain talent, outsourcing shifts the burden of hiring and retention to the provider while giving your business access to an entire team of specialists.
How to Choose the Right Managed Security Service Provider
Verify Provider Certifications
When evaluating managed security providers, start with their certifications—they reveal whether a provider follows the same security standards they promise to implement for you:
SOC 2 Type II confirms independent auditors have verified the provider's security, availability, and confidentiality controls over an extended period.
This matters because you're trusting them with access to your most sensitive systems.
ISO/IEC 27001 represents the international standard for information security management systems, indicating systematic management of sensitive information.
These certifications provide assurance that the MSSP follows rigorous security practices in their own operations—not just for client environments.
Evaluate Staff Qualifications
Certifications matter for the company, but the analysts actually monitoring your systems need verified expertise too. Look for:
- CISSP (Certified Information Systems Security Professional) from ISC2, demonstrating broad security knowledge
- CEH (Certified Ethical Hacker) showing understanding of attacker techniques
- Vendor-specific certifications for the tools they manage (Cisco, Microsoft, CrowdStrike, etc.)
- Ongoing training programs ensuring analysts stay current with evolving threats
Ask providers about their analyst qualifications, training programs, and staff retention rates.
Examine Service Level Agreements (SLAs)
Beyond the people and credentials, examine how providers commit to performance through their SLAs. These agreements define expectations and accountability—look for clearly defined metrics:
Mean Time to Detect (MTTD) measures how quickly they identify threats. Leading providers detect within minutes, not hours.
Mean Time to Respond (MTTR) measures how quickly containment procedures begin. Quality MSSPs start response immediately upon detection.
Escalation procedures: Clear processes for different severity levels, including who gets notified and when.
Uptime guarantees: Commitments to monitoring availability, typically 99.9% or higher.
Vague SLAs that promise "best effort" without specific timeframes are red flags.
Assess Integration and Scalability
The best managed security providers work with what you've already built. They should integrate with existing infrastructure—including physical security systems, network equipment, and access control—rather than demanding wholesale replacement:
- Compatibility with current firewalls, endpoints, and cloud services
- API integrations with business applications
- Support for your specific technology stack
- Ability to scale from single-site to multi-location operations as your business grows
Providers demanding proprietary solutions or infrastructure overhauls create vendor lock-in and drive up costs. This is especially important if you've invested in quality structured cabling and physical security infrastructure—the managed security layer should enhance, not replace, those foundations.
Consider Compliance Expertise
Finally, if regulations govern your industry, verify the provider has relevant compliance experience:
- HIPAA expertise for healthcare organizations
- PCI DSS knowledge for businesses handling payment cards
- GDPR understanding for companies with European customers
- Industry-specific frameworks relevant to your business
Providers with relevant compliance experience can generate audit documentation, support regulatory assessments, and ensure security controls meet specific requirements.
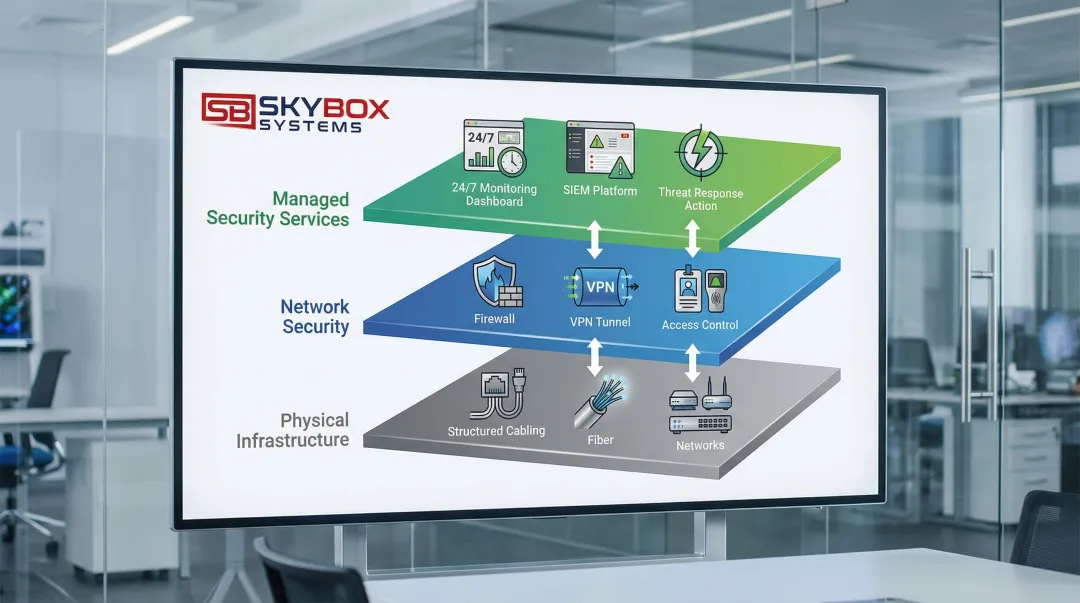
The Role of Infrastructure in Network Security
Physical Infrastructure as Security Foundation
Effective cybersecurity requires reliable physical infrastructure. Without it, even the most advanced security tools can't function properly.
Properly designed network infrastructure—including structured cabling, fiber optics, and network segmentation—creates the foundation for security controls to work effectively.
Structured cabling systems form the backbone of secure network operations, providing:
- Reliable connectivity that prevents security gaps from network outages
- Proper network segmentation capabilities to isolate sensitive systems
- Performance capacity to handle security monitoring traffic without degradation
- Physical security through controlled access to network infrastructure
Fiber optic infrastructure takes network security further with:
- High-speed connectivity for data-intensive security monitoring and log transmission
- Immunity to electromagnetic interference that could disrupt security systems
- Greater distance capabilities for campus and multi-building environments
- Enhanced security against physical tapping compared to copper cabling
Integrated Physical and Digital Security
When access control systems and network security share infrastructure, organizations gain unified protection that responds faster and more intelligently:
- Unauthorized physical access attempts trigger network security alerts
- Video surveillance integrates with security event timelines for investigation
- Physical access credentials can be automatically revoked when network compromises are detected
- Single management platforms reduce complexity and improve response coordination
Skybox Systems designs integrated systems where physical security infrastructure and network security share common platforms. This integration eliminates the disconnected silos that slow incident response and create visibility gaps.
Infrastructure Standards and Security
Infrastructure certifications matter because they ensure your network foundation won't undermine your security investments. These credentials indicate a provider's commitment to best practices that support long-term security, performance, and troubleshooting:
BICSI (Building Industry Consulting Service International): Ensures technicians follow industry standards for structured cabling design and installation, creating infrastructure that supports current and future security needs.
TIA/EIA Standards: Compliance with Telecommunications Industry Association and Electronic Industries Alliance standards ensures infrastructure meets performance specifications and supports proper network segmentation.
Panduit Certified Installers: Manufacturer certifications demonstrate expertise with specific infrastructure components and adherence to installation best practices.
These certifications matter because improperly installed infrastructure creates performance issues, security gaps, and troubleshooting challenges that undermine even the best security tools.
Working with infrastructure specialists like Skybox Systems—who maintain BICSI, TIA, EIA, and Panduit certifications—ensures the physical foundation supports comprehensive security strategies. Since 2009, Skybox has provided integrated infrastructure and security solutions across Florida and Georgia, creating reliable, secure connectivity for businesses that demand both quality installation and long-term performance.
Frequently Asked Questions
What is the difference between managed network security and traditional IT security?
Traditional IT security involves in-house staff managing tools reactively. Managed security provides proactive 24/7 monitoring and threat response by specialized experts operating from dedicated Security Operations Centers.
How much do managed network security services typically cost?
Industry benchmarks indicate basic services average $45 per endpoint monthly, while premium services average $73 per endpoint monthly. This is significantly less than hiring full-time security staff and purchasing enterprise tools, which can exceed $2.5 million in the first year.
What should I look for when choosing a managed security service provider?
Evaluate provider certifications (SOC 2, ISO 27001), staff qualifications (CISSP, CEH), clearly defined SLAs with specific response times, and whether they offer integrated infrastructure and security solutions. Providers who understand both physical infrastructure and cybersecurity deliver more cohesive protection.
Can managed security services help with compliance requirements?
Most MSSPs provide compliance support including continuous monitoring documentation, audit preparation, and security controls aligned with HIPAA, PCI DSS, and GDPR. This satisfies regulatory requirements for log review and continuous assessment that are operationally burdensome for internal teams.
How quickly can a managed security provider respond to threats?
Quality MSSPs typically detect threats within minutes and begin response procedures immediately. Leading providers offer defined SLAs for different severity levels, with critical threats receiving immediate attention and lower-severity issues addressed within specified timeframes.
Do I still need in-house IT staff if I use managed security services?
Managed security complements rather than replaces internal IT teams. In-house staff focus on business-enabling projects and user support while security specialists handle threat monitoring and incident response, maximizing the value of both resources.